OPNsense Firewall Migration and Tuning
For the better part of 20 years, I’ve been using pfSense and its predecessor m0n0wall as my firewall both for running my business (office and data center) and home networks. A few days ago, following some licensing changes with pfSense, I decided to switch to OPNsense. I no longer have a business for which it makes sense to license pfSense, and the hobby user license is no longer a sensible choice. OPNsense has similar heritage and features along with a more favorable license, so it was an obvious option.
The migration was pretty straight forward. Unfortunately the two do not use the same config file format, but they are similar. To minimize downtime (and avoid being yelled at by everyone in the house working and streaming) I set up a virtual machine on my laptop and installed OPNsense. I then set about rebuilding the configuration from scratch, going section by section on my existing firewall.
The two stumbling blocks were IPv6 and IPSec VPN mobile clients. Both were resolved by finding some tutorials online to translate the old settings to the new ones.
Once all that was sorted out, I saved the config file to my laptop and then manually edited the interface names to match the real hardware device in the XML file. One thing that I was able to copy from the old pfSense config file was the encrypted passwords. Since they use the standard password encryption on FreeBSD, they were the same on both systems.
Armed with the updated config file, I was able to save it to a FAT32 formatted USB stick along with the USB stick for OPNsense. I plugged both into my firewall device and installed it with the configuration ready to go. Total downtime was about 15 minutes and I was able to do that early in the morning before the house was awake.
Tuning #
Out of the box, everything is auto-tuned really well for my home network use. Two settings I did change were to disable some of the mitigations for some Intel CPU bugs which are really only important on multi-user systems or virtualization host systems. The OPNsense documentation discusses other settings which may be of interest in balancing the hardening of the system with performance. The overall effect of changing these settings is estimated at about 10-15% improvement in CPU performance.
These are set in the System -> Settings -> Tunables section of the OPNsense configuration.
Turn off Spectre 2 Mitigation #
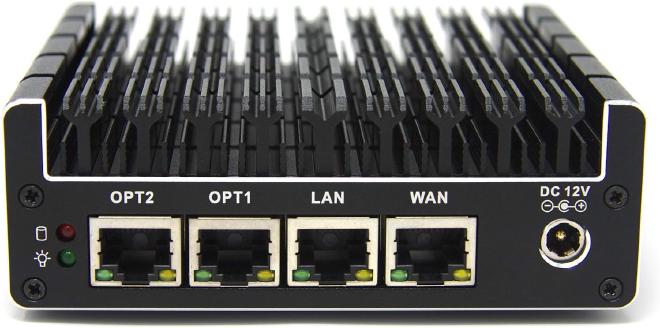
This mitigation is off by default on FreeBSD but enabled on OPNsense. On the Protectli Vault FW4C appliance I use, it is not active anyway because the hardware is not susceptible to it. I set it anyway in case I move to another hardware that does support it.
hw.ibrs_disable=1
Check the current value from the command line:
sysctl hw.ibrs_active
Turn off Meltdown Mitigation #
We’re not concerned with unknown binaries running on the system attacking it.
vm.pmap.pti=0
Reboot is required to change the PTI setting.